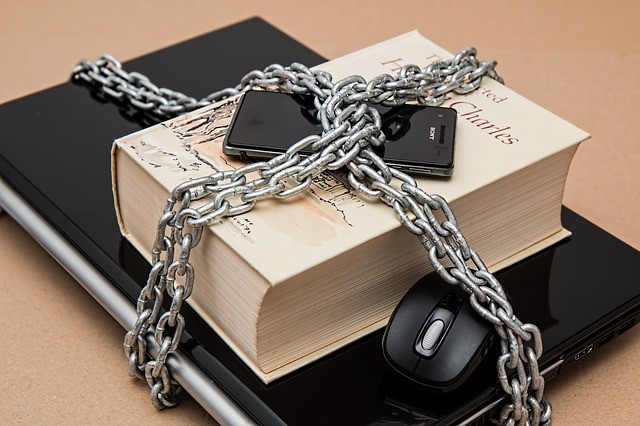
What to choose and what not to choose?
With over 1.5 million mobile apps to choose from on your phone, finding the ones that you need while maintaining your device’s security does pose a realistic problem to a growing proportion of people today. This figure increases by the thousand every week while ‘hot new apps’ are being highlighted in app stores with nothing more than a quick algorithm filter or review system to separate the good from the malicious.
These defensive actions from vendors don’t quite seem to be cutting it, as an average of 2,400 unsafe applications have been installed on the phones of employees working for large enterprises. In this case, these unsafe applications either expose sensitive data, perform activities that are suspicious like recording phone calls, and share employee personal information with a third party. Additionally, this study looked into hundreds of thousands of mobile applications currently running on corporate devices.
How are all these unsafe apps getting on your phone?
Many people like to consider the apple app store as the best in mobile app security because of their application screening process automatically looks at every app before approving it for store implementation. Of course, this process can only do so much when it is up against having to look at the minute details within an application’s coding, so the cracks aren’t exactly hard to slip through, especially for malicious activities that phish for your personal data.
On the other hand, Android give its security controls mostly over to the consumer with an extensive review system. Needless to say, this type of system has innate flaws within itself.
So where do all these unsafe apps originate?
Because so many mobile app developers out there recognize that the “from scratch” coding process can take a huge amount of time, free code is utilized from all over the internet. With only a small snippet of code inserted into a functional segment of an app’s development, a hacker can pull information from mobile app users after it is installed onto a phone without the developer even knowing.
Other sources of risk for smartphone applications
A significant reason that mobile applications are targeted more than their counterparts on the desktop, is because mobile applications create a temporary cache of information to make your device perform faster. Unfortunately, this cache is especially easy for hackers to pull information from as it can feed directly from your smartphone application. To try to solve this issue, developers can either require a password to be created for their app, or the user can create automatic cache deletion function to wipe the application each time it restarts.
Another issue for mobile app users is the implementation of outdated or non-existent encryption methods. Because applications often hold very sensitive data like credit cards, it goes without saying that modern effective encryption algorithms are a must-have.
What is it that you can do?
Undoubtedly, mobile applications are growing in popularity, but they are similarly growing in risk. It’s becoming quite common for mobile app users have to ask themselves “How much do I trust the developer of this app?” before either installing or entering sensitive information into it. If you’re concerned about your mobile app’s security or privacy, it might be about time that you considered protecting it. There are actually quite a few methods that have been developed by modern techies looking to help people just like you.
Image credit: https://pixabay.com/en/censorship-limitations-610101
About ISHIR:
ISHIR is a Dallas Fort Worth, Texas based AI-Native System Integrator and Digital Product Innovation Studio. ISHIR serves ambitious businesses across Texas through regional teams in Austin, Houston, and San Antonio, along with presence in Singapore and UAE (Abu Dhabi, Dubai) supported by an offshore delivery center in New Delhi and Noida, India, along with Global Capability Centers (GCC) across Asia including India (New Delhi, NOIDA), Nepal, Pakistan, Philippines, Sri Lanka, Vietnam, and UAE, Eastern Europe including Estonia, Kosovo, Latvia, Lithuania, Montenegro, Romania, and Ukraine, and LATAM including Argentina, Brazil, Chile, Colombia, Costa Rica, Mexico, and Peru.
ISHIR also recently launched Texas Venture Studio that embeds execution expertise and product leadership to help founders navigate early-stage challenges and build solutions that resonate with customers.
Get Started
Fill out the form below and we'll get back to you shortly.