There are now officially 10 billion devices connected to the Internet of Things. These devices include voice controllers, health and fitness trackers, smartwatches, smart security systems, and smart appliances. These devices all have unique identifiers and the capability to send information over networks without any human intervention. This information often goes straight to a user’s smartphone and the smartphone can, in turn, directly control the devices. The Internet of Things is an over $250 billion and growing market.
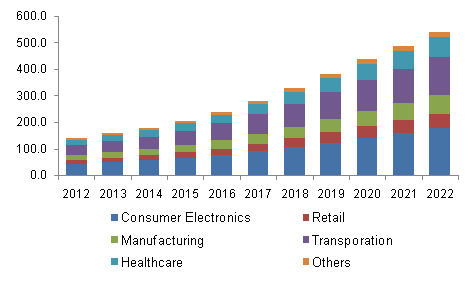
Source: Grand View Research, Inc.
The rapid proliferation of IoT devices has also led to a host of new security issues. IoT security should not be taken lightly. Governments, organizations, and individuals have not yet properly adjusted to these changes and found ways to mitigate these risks. Here are the 7 most pressing security threats to IoT and the protective measures you need to take:

The Six Biggest Security Threats and Challenges for IoT:
1. Devices Used To Spy On People
The most frightening use of IoT devices and the one that has captured the most media attention is spying. IoT products usually contain some form of camera and microphone, as well as a log of the times of the day they have been used. These devices are then placed in sensitive environments such as inside houses, throughout businesses, and on individual persons during the course of their day. The combination of their weak security protocols and dangerous amounts of access can lead to disaster. There have been many high profile incidents of IoT devices spying on their owners.
2. Hackable API And Backend Interfaces
The interfaces on IoT devices often lack encryption, input-output traffic filtering, and authentication. These weak APIs can often hand over the reins of the system to malicious third-parties. Hackable backends have been exploited in ways that put people’s lives at serious risk. They have shown the ability to take control of autonomous driving vehicles and crash them. In medical devices such as pacemakers, hackers have been able to remotely turn off these devices.
3. Insecure Update Mechanism
IoT devices need the capability to securely update when a change to the operating system is needed. First, the IoT product should alert customers when a security update is available and recommend that the update is installed as soon as possible. Many IoT devices have no firmware validation at all.
4. SQL Injections
SQL injections are a type of computer virus, a form of code injections. Code injections tell a software program to process invalid and malicious data. This data can lead to more viruses and change the way the software functions. Eventually, these systems can perform privilege escalation and can gain access to administrator files. SQL injection is a form of this attack that utilizes SQL statements in a database entry field. These attacks threaten the security of crucial information in the system’s database.
5. Inability To Implement Firewalls
Both personal computers and IoT devices need firewalls. A firewall watches internal network traffic to prevent misuse from an external network, usually the internet. Firewalls keep packets of information filtered. Both forms of hardware need to filter packets equally as much but both forms do not perform equally as well. IoT devices often lack the ability to implement a firewall because of their low processing power. Typical firewalls have been designed for use on large servers and are not implementable on IoT devices.
6. Used In DDoS Attack
Your own IoT device might be used to facilitate a DDoS attack. Hackers can install viruses on weakly secure IoT devices to develop a botnet that can be ready for later used. These zombie devices can be remotely activated to trigger a denial of service attack against a server. These attacks work by overwhelming the server with illegitimate requests. The systems must slow down for all users, including genuine ones, to accommodate these false requests. IoT devices are the perfect DDoS bots for hackers and often very easy to acquire.
7. Weak Passwords
Do you know the passwords for all your IoT devices? Probably not, and that could be a huge problem. IoT devices often have weak, guessable, and even hardcoded passwords. These passwords are often unknown to the users of the devices. 2-layer security is often impossible. Hackers find it extremely easy to gain access to such devices.
Internet of Things (IoT) security: 7 ways you can help protect yourself
1. Change Passwords
Many people forget that passwords on IoT devices work exactly the same as passwords on other computers. One of the most important rules of password protection is to change passwords regularly. By regularly, we mean at least twice a year and much more if the device holds important information or you have reason to suspect an intrusion. A unique password should be used for every device.
2. Physical Hardening
Computer systems need physical hardening methods to limit the surface of vulnerability, which is the sum of all the systems attack vectors. Physical hardening must be built into every IoT device you use. The lack of physical hardening engineers with knowledge of IoT means that extra precautions should be made to find an expert.
3. Monitor Devices For Physical Compromises
Watch your devices to make sure that they haven’t been tampered with. This is one of the easiest ways for bad actors to gain access to your device. Check all input sources to your device as well as any factory reset switches. Know who has access to your devices and avoid leaving them alone and unsecured. If you believe your device has been tampered with, take it immediately to a security professional.
4. Turn Off Automatic Wifi Connection
You’ll only want your device to connect to wifi if you already know that the network is secure. Many IoT devices come preset to automatically connect to wifi networks they are near during the day. These networks can steal the information you generate during the course of your usage. This is very risky for situations such as online banking transactions. Turning off this connection can prevent this risk that often happens while users are completely unaware.
5. Update Your Device
As already mentioned, IoT devices have inconsistent security updates and weak update alert systems. Users must take their own prerogative to find out the update schedule of their device and keep it updated as soon as possible. An update often comes after a known threat has been detected. Every day a system is not updated increases the risk to the system. By installing the updates as soon as possible, you will be ready for the risks on any network.
6. Deactivate Features You Don’t Use
Items with superfluous features only pose a security risk. It’s best that all cameras and microphones not in use are turned off and disabled. This can often be done with simple fixes. This technology is now on smart watches, smart tvs, and other household appliances. Avoid systems like smart speakers that use passive speech monitoring if possible, if not possible use only trusted manufacturers or retailers.
7. Work With The Pros
Expertise on IoT devices is still rare. On any software development project involving IoT, utilizing trusted and experienced professionals is the key to preventing security issues. Find developers with certifications such as Microsoft Partners. These developers are equipped to handle the complicated and quickly changing requirements of IoT security.
What to Do
The new security risks that come with IoT devices are nothing to take lightly. A weak security implementation will always cost you more in the long run. The process of developing secure systems starts on day 1 and the maintenance should go on throughout the life of your product. Only a cybersecurity expert can mitigate these threats and build you a secure system. You need a partner with experience and knowledge to get the job done. ISHIR is the world’s leading team in cybersecurity and IoT device design. Contact our IoT Solution Experts today for an evaluation of your security needs!
About ISHIR:
ISHIR is a Dallas Fort Worth, Texas based AI-Native System Integrator and Digital Product Innovation Studio. ISHIR serves ambitious businesses across Texas through regional teams in Austin, Houston, and San Antonio, along with presence in Singapore and UAE (Abu Dhabi, Dubai) supported by an offshore delivery center in New Delhi and Noida, India, along with Global Capability Centers (GCC) across Asia including India (New Delhi, NOIDA), Nepal, Pakistan, Philippines, Sri Lanka, Vietnam, and UAE, Eastern Europe including Estonia, Kosovo, Latvia, Lithuania, Montenegro, Romania, and Ukraine, and LATAM including Argentina, Brazil, Chile, Colombia, Costa Rica, Mexico, and Peru.
ISHIR also recently launched Texas Venture Studio that embeds execution expertise and product leadership to help founders navigate early-stage challenges and build solutions that resonate with customers.
Get Started
Fill out the form below and we'll get back to you shortly.



